HoHo … No
Details
- Location: KringleCon/Santa's Office
- Elf: Eve Snowshoes
Elf's Objective Message
Hey there, how's it going? I'm Eve Snowshoes.
Lately I've been spending a lot of cycles worrying about what's going on next door. Before that, I was checking out Fail2Ban. It's this slick log scanning tool for Apache web servers. If you can complete this terminal challenge, I’d be happy to give you some things I’ve learned about Kerberoasting and Active Directory permissions! Why don't you do some work with Fail2Ban on this Cranberry Pi terminal first, then we’ll talk Kerberoasting and Active Directory. OK?
This terminal is located in Santa's Office at KringoleCon. Solving this terminal challenge provides additional hints for objective 8. To view the hints for this terminal challenge use the menu on the left.
To solve this terminal challenge you need to configure Fail2Ban to automatically create a 'naughty lists' of IPs based on brute forcing and password spraying attempts.
You will need to create three files for Fail2Ban to solve this challenge, a jail file, an action file, and a filter file. You will need to create these files based on the description provided in this challenge.
You will need to create a jail file, /etc/fail2ban/jail.d/santa_jail.conf, to specify the log file fail2ban needs to monitor and the parameters that qualify an IP address for the naughty list.
/etc/fail2ban/jail.d/santa_jail.conf
You will need to create an action file, /etc/fail2ban/action.d/naughtynice_action.conf, to specify what fail2ban should do when a naughty IP address is found.
/etc/fail2ban/action.d/naughtynice_action.conf
You will need to create a filter file, /etc/fail2ban/filter.d/naughtynice_filter.conf, to specify how fail2ban should find the naughty IP addresses.
/etc/fail2ban/action.d/naughtynice_action.conf
Testing Tip
You can use fail2ban-regex to test out the regex you want to filter.
ex. fail2ban-regex '2021-12-18 20:00:39 Failed login from 43.243.8.109 for dasher' '^ Failed login from <HOST> for \w+$'
Remove Valid Enteries From Log
You can use egrep to filter out the valid log enteries. This will leave the entries that you need to triger on.
ex. egrep -v '(Login from\s+[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\s+successful$)|(Valid heartbeat from\s+[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}$)|([0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\: Request completed successfully$)|(Failed login from [0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3} for \w+$)|(Login from [0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3} rejected due to unknown user name$)' /var/log/hohono.log
To run fail2ban after creating/modifying the configuration files run the following commands:
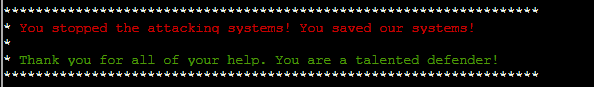
Once you've created the 3 files mentioned above and ran fail2ban as stated above, you will receive the following message: