Terminal - Scapy Prepper¶
Terminal¶
- Elf: Alabaster Snowball
- Location: Roof/Netwars
- Related to Objective: 9
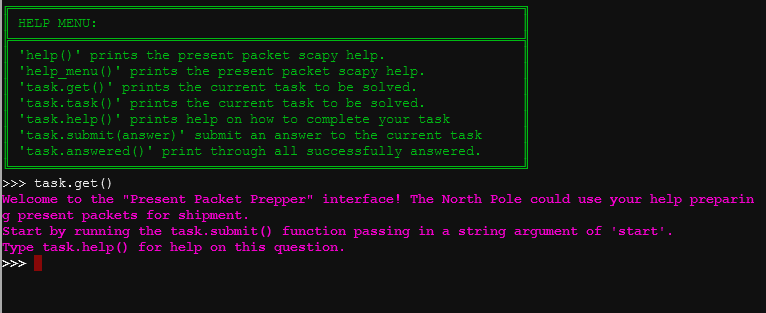
The goal of this terminal challenge is to teach you a little about networking and crafting packets. You get various tasks that you need to complete using scapy. Scapy documentation is very helpful for this task. If you run into a challenge, use the command task.help() to get hints.
Answer¶
Here are the answers for this challenge in order:
task.submit(send)
task.submit(sniff)
task.submit(1)
task.submit(rdpcap)
task.submit(2)
task.submit(UDP_PACKETS[0])
task.submit(TCP_PACKETs[1][TCP])
UDP_PACKETS[0][IP].src = "127.0.0.1"
task.submit(UDP_PACKETS[0])
task.submit("echo")
task.submit(ICMP_PACKETS[1][ICMP].chksum)
task.submit(3)
packet=IP(dst="127.127.127.127")/UDP(dport=5000)
task.submit(packet)
dns_query = IP (dat="127.2.3.4")/UDP(dport=53)/DNS(rd=1,qd=DNSQR(qname=elveslove.santa"))
task.submit(dns_query)
ARP_PACKETS[1][ARP].hwdst="00:16:ce:6e:8b:24"
ARP_PACKETS[1][ARP].hwsrc="00:13:46:0b:22:ba"
ARP_PACKETS[1][ARP]=2
task.submit(ARP_PACKETS)
After you complete the challenge, Alabaster Snowball tells you the following:
Oh, I see the Scapy Present Packet Prepper has already been completed! Now you can help me get access to this machine. It seems that some interloper here at the North Pole has taken control of the host. We need to regain access to some important documents associated with Kringle Castle. Maybe we should try a machine-in-the-middle attack? That could give us access to manipulate DNS responses. But we'll still need to cook up something to change the HTTP response. I'm sure glad you're here Santa.